IEC TC65 Releases Cybersecurity Validation Guide for Industrial Instruments
On May 8, 2026, the International Electrotechnical Commission (IEC) Technical Committee 65 published IEC TR 63373:2026 — Guidance on Cybersecurity Validation for Industrial Instruments, introducing standardized approaches to firmware signing, remote configuration audit trails, and encrypted OT protocol transmission. The release signals a tightening of cybersecurity expectations across industrial automation, with immediate implications for manufacturers, integrators, and operators in process-critical sectors.

Event Overview
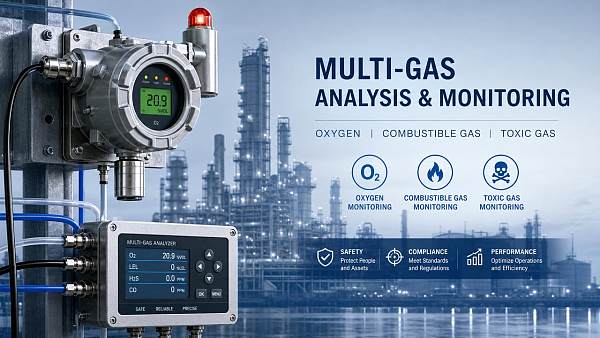
The International Electrotechnical Commission (IEC) TC65 issued IEC TR 63373:2026 on May 8, 2026. The technical report provides implementation guidance for validating cybersecurity capabilities in field instruments—including digital pressure transmitters, flow meters, temperature sensors, and valve positioners—focusing specifically on firmware signature verification, remote configuration change auditing, and encryption of industrial communication protocols (e.g., HART-IP, Modbus TCP, OPC UA over TLS). Separately, China’s national standard GB/T 42278-2026, which adopts IEC TR 63373:2026 with national modifications, entered the final review stage at the Standardization Administration of China (SAC) on May 10, 2026, and is expected to be officially released in June 2026.
Industries Affected
Direct Export/Import Enterprises
Export-oriented instrumentation vendors targeting EU, US, and ASEAN markets face accelerated compliance pressure: while IEC TR 63373:2026 is not mandatory, it is increasingly referenced in procurement specifications by major end-users (e.g., oil & gas majors, pharmaceutical OEMs) and may soon inform conformity assessment under the EU Cyber Resilience Act (CRA). For Chinese exporters, alignment with GB/T 42278-2026 will become a de facto market access requirement for domestic public-sector tenders and state-owned enterprise projects starting Q3 2026.
Raw Material & Component Suppliers
Suppliers of secure microcontrollers (e.g., ARM TrustZone-enabled SoCs), cryptographic modules, and trusted platform modules (TPMs) are seeing revised qualification requirements from instrument OEMs. Notably, the guide mandates hardware-rooted trust anchors for firmware signature validation—shifting demand toward components pre-certified to Common Criteria EAL4+ or NIST SP 800-193. Suppliers lacking documented supply-chain integrity controls (e.g., SBOM generation, firmware provenance tracking) may face disqualification during OEM vendor audits.
Instrument Manufacturing Enterprises
Manufacturers must now embed security validation into product development lifecycles—not just as a final test, but as an integrated activity spanning design, firmware build, and field update processes. Key operational impacts include: (1) adoption of signed firmware delivery pipelines; (2) integration of immutable audit logs for configuration changes (including timestamps, operator IDs, and change deltas); and (3) mandatory transport-layer encryption for all remote management interfaces—even when deployed within air-gapped networks, per the guide’s risk-based rationale.
Supply Chain Service Providers
Third-party cybersecurity validation labs, certification bodies, and OT-focused managed security service providers (MSSPs) are adjusting scope documentation to cover instrument-specific test cases outlined in the guide—particularly those related to protocol-level encryption resilience and firmware rollback protection. Meanwhile, logistics and customs brokers handling instrument shipments may soon require updated technical declarations referencing GB/T 42278-2026 compliance status, especially for government-funded infrastructure projects in China.
Key Focus Areas and Recommended Actions
Conduct Gap Assessment Against IEC TR 63373:2026 Annex A
Organizations should map existing firmware signing workflows, remote access logging mechanisms, and OT protocol encryption coverage against the 12-point validation checklist in Annex A of the guide. Prioritize remediation where cryptographic agility (e.g., support for post-quantum signatures) or audit log immutability is missing.
Engage Early with SAC-Accredited Testing Labs
With GB/T 42278-2026 entering final review, accredited laboratories—including China Electronics Standardization Institute (CESI) and Shanghai Institute of Measurement and Testing Technology (SIMT)—are preparing test protocols. Manufacturers are advised to initiate pre-assessment engagements before June 2026 to avoid bottlenecks during formal certification.
Update Supplier Agreements to Include Security Artifacts
Procurement contracts for microcontrollers, communication ICs, and embedded OS vendors should explicitly require provision of SBOMs, firmware build attestations, and cryptographic key management documentation—aligning with Clause 5.2 of the guide’s supply chain assurance framework.
Editorial Perspective / Industry Observation
Analysis shows this is not merely a ‘cyber hygiene upgrade’ but a structural shift toward accountability-by-design in industrial instrumentation. Observably, IEC TR 63373:2026 treats firmware integrity and configuration traceability as foundational—not optional add-ons—thereby raising the bar for legacy instrument modernization programs. From an industry perspective, the timing coincides with rising regulatory scrutiny of OT cyber incidents in critical infrastructure; however, current guidance remains voluntary and non-prescriptive on enforcement mechanisms. That said, its rapid national adoption in China—and likely reference in upcoming EU Type Examination schemes—suggests early alignment carries competitive advantage beyond compliance.
Conclusion
This development marks a maturation point in industrial cybersecurity standardization: moving from network perimeter defense to device-level assurance. While full regulatory enforcement remains jurisdiction-dependent, the convergence of IEC guidance and national standardization signals that cybersecurity validation is becoming a non-negotiable element of instrument specification, procurement, and lifecycle support. Rational observation indicates that proactive adaptation—especially in firmware governance and supply chain transparency—will define market leadership more than technical feature differentiation alone.
Source Attribution
Primary sources: IEC TC65 Secretariat (Publication Notice No. TC65/2026-017, dated May 8, 2026); Standardization Administration of China (SAC) Public Review Calendar, Entry No. GB/T 42278-2026-20260510. Pending items under observation: (1) official publication date and effective date of GB/T 42278-2026; (2) inclusion of IEC TR 63373:2026 references in revision drafts of IEC 62443-4-2 (Security for Industrial Automation and Control Systems); (3) potential linkage to EU CRA conformity assessment modules for programmable industrial devices.
Recommended for You
Search Categories
Search Categories
Latest Article
- First Global White Paper on Dynamic Calibration for Humanoid Robot Sensors ReleasedFirst global white paper on dynamic calibration for humanoid robot sensors—key for pressure & 6-axis force/torque accuracy in smart manufacturing and collaborative robotics.Posted by:
- FDA Updates IVD Import Guidelines: CNAS/NIST Calibration Chain RequiredFDA mandates CNAS/NIST calibration chain for IVD pressure & temperature sensors—key for Chinese exporters. Act now to meet July 2026 deadline.Posted by:
- EU PEF Carbon Database Mandatory Access for Chinese Industrial InstrumentsEU PEF Carbon Database mandatory for Chinese industrial instruments—meet June 15, 2026 deadline to keep CE marking & win EU tenders.Posted by:
Please give us a message