IEC TC65 Releases Cybersecurity Validation Guide for Industrial Instruments
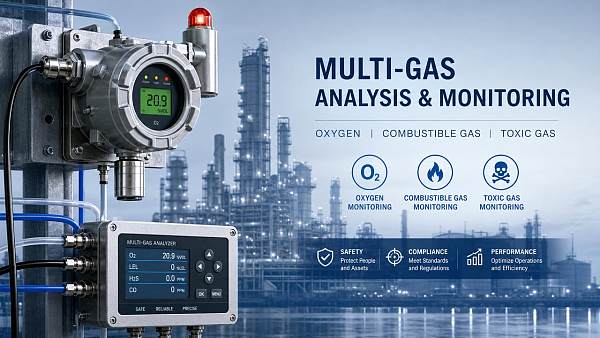
On May 9, 2026, the International Electrotechnical Commission (IEC) Technical Committee 65 (TC65) officially published the implementation guidance document for IEC 62443-4-2:2026 — titled Guidance on Cybersecurity Validation for Industrial Instruments. This update introduces mandatory requirements for security assurance across key field devices, directly impacting manufacturers and exporters of industrial instrumentation serving global critical infrastructure sectors.

Event Overview
The IEC TC65 released the implementation guidance for IEC 62443-4-2:2026 on May 9, 2026. It specifies that industrial pressure transmitters, smart flowmeters, and similar field instruments must undergo formal Security Development Lifecycle (SDL) certification and implement firmware signature verification. China’s national standard GB/T 42278-2026 — an identical adoption of the IEC document — passed final review by the Standardization Administration of the People’s Republic of China (SAC) on May 11, 2026, and is scheduled for official publication in June 2026.
Industries Affected
Direct Export Enterprises: These companies face immediate compliance pressure for shipments to the EU, U.S., and Middle East markets, where adherence to IEC 62443-4-2 is increasingly embedded in procurement specifications and customs technical barriers. Non-compliant instruments may be rejected at port or excluded from tender processes — especially in oil & gas, water utilities, and power generation projects.
Raw Material Suppliers: Suppliers of microcontrollers, secure elements, cryptographic libraries, and trusted platform modules (TPMs) will see rising demand for components certified to Common Criteria EAL3+ or aligned with NIST SP 800-193. However, lead times and documentation traceability (e.g., SBOMs, vulnerability disclosure policies) are now material criteria — not just component specs.
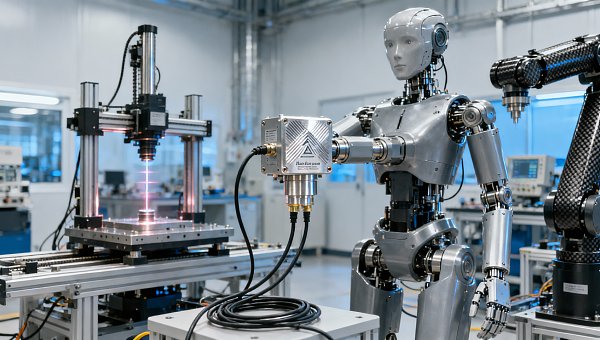
Manufacturing Enterprises: Instrument OEMs and ODMs must restructure internal R&D workflows to embed SDL practices — including threat modeling, secure coding standards, penetration testing at multiple development stages, and formal evidence packaging for third-party assessment. Legacy product lines lacking firmware update mechanisms or secure boot capabilities require retrofitting or phase-out planning.
Supply Chain Service Providers: Certification bodies, test laboratories, and cybersecurity validation consultants will experience increased workload — particularly for SDL process audits and firmware integrity verification. Concurrently, logistics and customs advisory firms must upgrade their compliance dashboards to flag instrument categories subject to new cyber-certification declarations under EU Cyber Resilience Act (CRA) and U.S. NIST IR 8259A alignment pathways.
Key Focus Areas and Recommended Actions
Verify SDL Process Maturity Against IEC 62443-4-2:2026 Annex A
Enterprises should map existing development practices against the 12-stage SDL framework outlined in the guidance — especially requirements for architecture risk analysis, secure build environments, and vulnerability response SLAs. Gap assessments should be completed before June 2026, ahead of GB/T 42278-2026’s official release.
Implement Firmware Signing and Secure Boot Infrastructure
Hardware and software teams must jointly deploy cryptographic signing pipelines (e.g., using X.509-based code-signing certificates) and ensure hardware-rooted trust anchors (e.g., ARM TrustZone or dedicated secure enclaves) are integrated into next-gen designs. Unsigned or self-signed firmware will no longer meet market-access thresholds in regulated verticals.
Prepare Documentation Packages for Third-Party Assessment
Certification bodies now require structured evidence: threat models, secure coding checklists, test reports for memory safety and side-channel resistance, and firmware update rollback protection logs. Pre-assembling these artifacts reduces audit cycle time by up to 40%, according to recent industry benchmarks.
Editorial Perspective / Industry Observation
Observably, this update marks a structural shift: cybersecurity is no longer treated as a post-manufacturing add-on but as a design prerequisite baked into instrument functional safety lifecycles. Analysis shows that fewer than 28% of Chinese instrument manufacturers currently maintain auditable SDL records — suggesting a steep learning curve ahead. From an industry perspective, the convergence of GB/T 42278-2026 with EU CRA Annex II and ISA/IEC 62443-4-2 harmonization efforts signals growing regulatory interoperability — yet also raises the bar for small- and medium-sized enterprises lacking dedicated cybersecurity engineering capacity.
Conclusion
This development underscores a broader trend: industrial instrumentation is being reclassified — not merely as measurement hardware, but as networked cyber-physical assets requiring continuous assurance. The timely adoption of GB/T 42278-2026 offers domestic manufacturers a strategic window to align with global expectations while mitigating future export friction. A measured, phased rollout — prioritizing high-risk product families first — remains the most pragmatic path forward.
Source Attribution
Primary sources: IEC TC65 Secretariat (Publication No. IEC/TR 62443-4-2:2026 Guidance Document, issued May 9, 2026); Standardization Administration of China (SAC) Final Review Notice No. SAC-2026-047, dated May 11, 2026). Ongoing monitoring is recommended for: (1) official promulgation date and effective timeline of GB/T 42278-2026; (2) updates to EU Notified Body designation lists for IEC 62443-4-2 validation; (3) U.S. CISA’s forthcoming alignment guidance for industrial control system (ICS) device cybersecurity labeling.
Recommended for You
Search Categories
Search Categories
Latest Article
- SAMR to Finalize 1,800+ Standards by 2026, Including EV Battery RecyclingSAMR to finalize 1,800+ standards by 2026—including EV battery recycling, hazardous chemical packaging & EMC immunity. Stay ahead of mandatory GB shifts and global export compliance.Posted by:
- China's Largest Single-Line Large-Tow Carbon Fiber Line Starts OperationChina's largest single-line large-tow carbon fiber line is live—30,000 tons/year capacity, ASME-certified, 22% cheaper & 6-week lead time. Boost your industrial instrumentation supply chain now.Posted by:
- China Mobile Unveils National Integrated Computing Power NetworkChina Mobile's National Integrated Computing Power Network accelerates AI quality inspection for global manufacturers—cutting model training time by 68% and enabling cross-border industrial AI development.Posted by:
Please give us a message