IEC 62443-4-2:2026 CDV Adds China Supply Chain Transparency Clause
On April 16, 2026, IEC TC65 published the Committee Draft with Vote (CDV) for IEC 62443-4-2:2026, introducing a new clause — 7.3.5 ‘Supply Chain Transparency Requirements’ — mandating disclosure of origin, foundry, and Tier-2 supplier names for critical components (including FPGA, MCU, and cryptographic chips), plus CNAS accreditation status and China’s Cybersecurity Level Protection (MLPS 2.0) filing numbers for domestic suppliers. Industrial automation manufacturers, DCS/PLC vendors, and smart instrument suppliers targeting international critical infrastructure projects should closely monitor this development.
Event Overview
The International Electrotechnical Commission’s Technical Committee 65 (IEC TC65) released the CDV for IEC 62443-4-2:2026 on April 16, 2026. The draft includes a newly added Clause 7.3.5 titled ‘Supply Chain Transparency Requirements’. Under this clause, applicants seeking certification under IEC 62443-4-2 must disclose the country of origin, semiconductor fabrication facility (foundry), and names of Tier-2 suppliers for key hardware components — specifically listing FPGA, microcontroller units (MCU), and cryptographic chips. For suppliers located in China, applicants must further provide their China National Accreditation Service (CNAS) accreditation status and their official filing number under China’s Cybersecurity Level Protection 2.0 regime.
Industries Affected by This Update
Industrial Automation Equipment Manufacturers (e.g., DCS, PLC, Safety Controllers)
These firms are directly affected because IEC 62443-4-2 certification is often required for participation in international critical infrastructure tenders (e.g., power generation, oil & gas, water treatment). The new clause increases documentation burden and may delay certification timelines if supply chain data — especially from Chinese Tier-2 or component-level suppliers — is incomplete or lacks verified CNAS/MLPS 2.0 evidence.
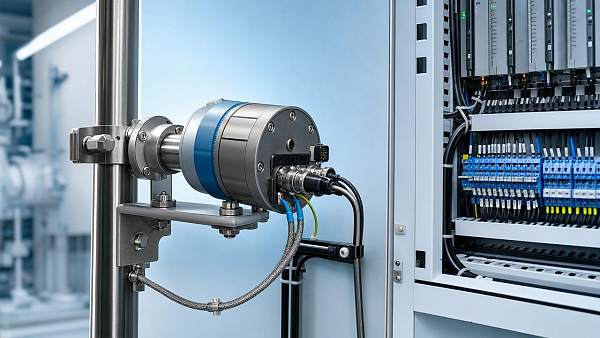
Smart Instrument and Field Device Suppliers
Vendors of intelligent pressure transmitters, flow meters, and safety shutdown devices relying on imported or domestically sourced MCUs/FPGAs face heightened scrutiny. Certification readiness now depends not only on their own development processes but also on traceability and compliance verification across upstream component providers — particularly those operating within China’s industrial ecosystem.
China-Based Component Distributors and Subcontractors
Distributors supplying FPGA, MCU, or crypto-chip modules to certified equipment makers must now prepare verifiable documentation: proof of origin, foundry identity, and — where applicable — CNAS accreditation scope and MLPS 2.0 filing confirmation. Absence of such documentation may render their components non-qualifiable for certified end-products.
What Enterprises and Practitioners Should Monitor and Do Now
Track official IEC TC65 feedback and finalization timeline
The CDV stage allows national committees to submit comments until the voting deadline. Current more than ever, stakeholders should monitor official IEC TC65 communications and national committee positions — especially those from China (SAC/TC124), Germany (DKE), and the U.S. (ANSI/NEMA) — as consensus outcomes will shape enforceable requirements.
Map critical components against Clause 7.3.5 scope and verify Chinese supplier documentation
Manufacturers should identify all FPGA, MCU, and cryptographic chips used in certified product lines and audit corresponding Chinese suppliers for active CNAS accreditation (with scope covering relevant testing or manufacturing activities) and valid MLPS 2.0 filing numbers. This is not a general cybersecurity assessment — it is a specific, documentable eligibility criterion.
Distinguish between policy signal and operational requirement
Analysis来看, this clause reflects growing regulatory emphasis on supply chain provenance in industrial control systems — particularly where geopolitical risk assessments intersect with technical assurance. However, it remains a CDV; its inclusion in the final standard is not guaranteed. Stakeholders should treat it as a high-probability signal, not an immediate compliance mandate.
Prepare internal cross-functional coordination between R&D, procurement, and quality teams
Effective response requires alignment across engineering (component selection), procurement (supplier onboarding and data collection), and quality/compliance (certification documentation management). Establishing a shared component traceability register — including foundry ID, Tier-2 names, and Chinese supplier compliance records — is a practical first step ahead of formal adoption.
Editorial Perspective / Industry Observation
From industry angle, this update signals a structural shift: IEC 62443-4-2 is evolving from a purely development lifecycle standard toward one embedding supply chain governance criteria — with explicit regional compliance hooks. It is better understood as a forward-looking policy signal rather than an implemented rule. Its significance lies less in immediate enforcement and more in previewing how future international certification frameworks may integrate jurisdiction-specific assurance mechanisms. Continuous monitoring is warranted — not because the clause is final, but because its inclusion in a CDV reflects broad technical committee endorsement of supply chain transparency as a foundational security attribute.
Conclusion: This CDV does not yet change certification rules, but it introduces a concrete, actionable dimension of supply chain accountability — anchored in verifiable documentation from Chinese suppliers. It is best interpreted as an early indicator of tightening interoperability conditions for industrial control products entering global critical infrastructure markets. Pragmatic engagement — focused on traceability mapping and documentation readiness — is more valuable at this stage than reactive compliance planning.
Information Source: IEC TC65 Official CDV Publication (IEC 62443-4-2:2026 CDV, issued April 16, 2026). Note: Final standard text, effective date, and implementation guidance remain pending; ongoing observation of IEC TC65 ballot results and national committee submissions is recommended.
Recommended for You
Search Categories
Search Categories
Latest Article
- FDA Updates IVD Import Guidance: CNAS Calibration Chain Required for China-Made DevicesFDA now requires CNAS calibration chain reports for China-made IVD analyzers—pH, ion & clinical chemistry devices entering via 510(k)/De Novo. Act now to avoid U.S. port rejections.Posted by:
- EN 61000-6-4:2026 Enters Force: Stricter EMC Requirements for Industrial Field InstrumentsEN 61000-6-4:2026 enforces stricter EMC requirements for industrial field instruments—key for AI edge controllers, sensors & exporters. Act now to ensure CE-EMC compliance by Nov 2026.Posted by:
- Global Methanol Electric Alliance Launches Cross-Border Energy Efficiency Recognition RoadmapGlobal Methanol Electric Alliance launches cross-border energy efficiency recognition roadmap—key for exporters, cal labs & methanol-instrument manufacturers.Posted by:
Please give us a message